Find Sensitive Data Everywhere. So You can protect it anywhere.
ML-POWERED DISCOVERY FOR MODERN AI & APPS
Protegrity’s dual-model approach finds sensitive data with high accuracy—including reliable discovery capabilities within the unstructured text that fuels modern AI and analytics use cases.
Chatbot Redaction
Automatically redact sensitive customer inputs (PII, PHI, etc.) within chatbot conversations in real time to ensure privacy and compliance—without adding friction to the customer experience.
Transcription Cleanup
Automatically remove sensitive information from call center transcripts or medical notes before storage, processing, or analysis—allowing those rich information streams to feed analytics and business intelligence applications.
GenAI RAG Pre-Processing
Scan and scrub sensitive information from documents before vectorization to prevent PII leakage into Retrieval-Augmented Generation (RAG) pipelines and LLM prompts.
App-Embedded Classification
Seamlessly integrate PII detection directly into app workflows via API/SDK to classify and protect data during ingestion, processing, or storage.
Unstructured Data Scanning
Go beyond structured databases to reliably find sensitive data hidden within free text fields, documents, emails, chatbot logs, and other unstructured data sources.
ADVANCED CLASSIFICATION & INTEGRATION FEATURES
THE LATEST
FROM PROTEGRITY
Protegrity Shares Perspective on Quantum Readiness and Post-Quantum Cryptography
Quantum computing may still be early for everyday enterprise use, but the security planning window is already open. In a recent InfoWorld article, industry experts explain how organizations can begin…
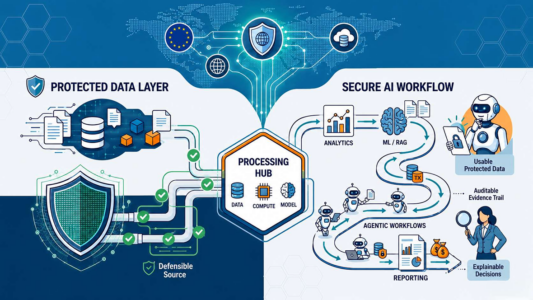
AI Security Starts With the Data Layer
A recent contributed article in The AI Innovator by James Rice, Vice President and AI Data Evangelist at Protegrity, examines why enterprise AI security must focus on the data and…
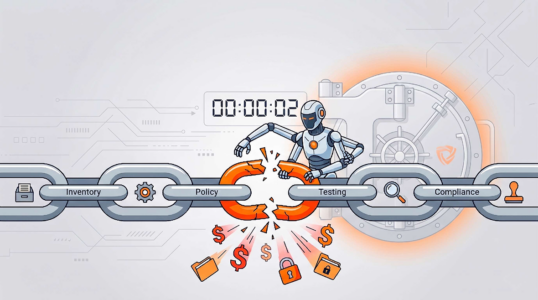
Protegrity on OpenAI Daybreak and Machine-Speed AI Security
A recent Cybersecurity Insiders article examines OpenAI’s introduction of Daybreak, a cybersecurity platform designed to autonomously discover and remediate vulnerabilities. The article frames the launch as part of a broader…
ENTERPRISE DATA SECURITY
IN A SINGLE PLATFORM
Discovery
Identify sensitive data (PII, PHI, PCI, IP) across structured and unstructured sources using ML and rule-based classification.
Learn MoreGovernance
Define and manage access and protection policies based on role, region, or data type—centrally enforced and audited across systems.
Learn moreProtection
Apply field-level protection methods—like tokenization, encryption, or masking—through enforcement points such as native integrations, proxies, or SDKs.
Learn morePrivacy
Support analytics and AI by removing or transforming identifiers using anonymization, pseudonymization, or synthetic data generation—balancing privacy with utility.
Learn more